Managed SOC services, or SOC as a service, provide organizations with a fully outsourced Security Operations Center (SOC). As a specialized SIEM provider and managed SOC partner, we oversee your entire digital environment, like networks, endpoints, cloud infrastructure, and applications, to resolve cyber threats in real time.
For UAE organizations with a shortage of cybersecurity talent and looking to safeguard their most critical digital assets, partnering with a SOC service provider is cost-effective and works wonders!
Finesse puts these worries to rest through our 24/7 Cognitive Security Operations Center(SOC), providing an economical, advanced solution no matter what your digital infrastructure needs.

Partnering with Finesse Cyberhub as your SOC service provider means enterprise-grade security without the cost or complexity of building it yourself. Here is what you get from day one.

A modern SOC is the main part of an organization’s defense plan. A Finesse-managed SOC includes:

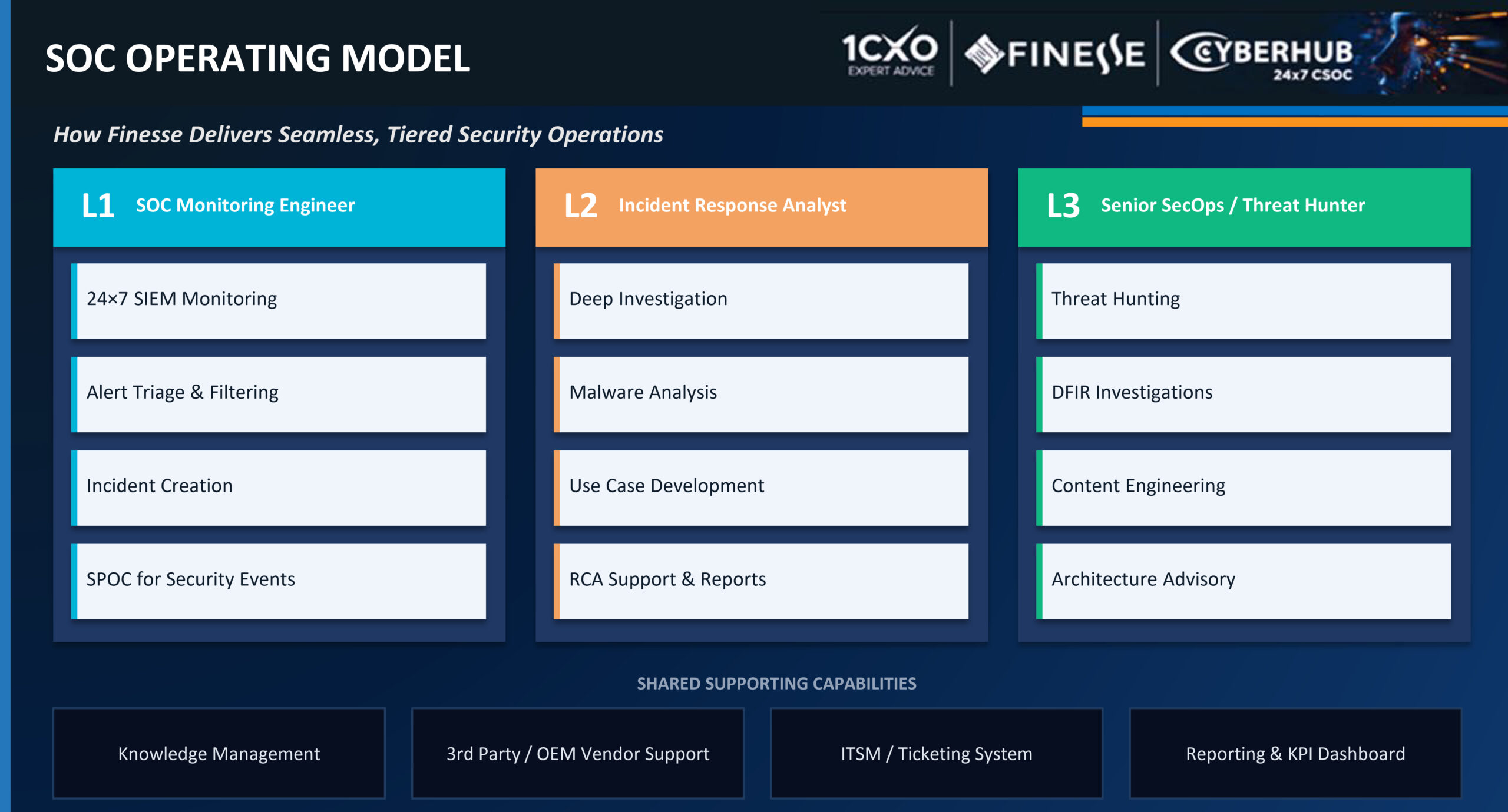
Every alert that enters our Cognitive SOC is handled through a structured three-tier model, ensuring the right analyst responds at the right level, with no gaps in coverage.
Centralized knowledge management, integrated ticketing, OEM vendor support, and KPI-driven reporting are all part of the operational backbone for all three tiers.

Our CSOC has a full set of tools to strengthen your defense-in-depth strategy:
We enable micro-segmentation and Zero Trust protocols. By utilizing PIM, PAM, and Multi-Factor Authentication (MFA), we ensure that no user, device, or application is implicitly trusted regardless of network location.


As a trusted SIEM provider and AI-native SOC partner, our experts combine the latest AI-native technology with localized threat intelligence, so security is never compromised.
Featured in Gulf News:
Finesse Cyberhub’s AI-native SOC transformation
Supporting cybersecurity initiatives across the GCC

A managed SOC keeps an eye on your environment all the time, but it works best when the weaknesses that attackers could use have already been found and fixed. That’s where VAPT services come in.
Finesse Cyberhub’s VAPT and Penetration Testing Services in Dubai and the UAE combine vulnerability assessment with active penetration vulnerability testing that simulates real-world attacks on your web apps, networks, cloud infrastructure, APIs, and mobile apps to find the holes in your defenses that haven’t been closed yet.
Managed SOC and VAPT work together to give you ongoing threat monitoring and proactive attack surface reduction, which are the two most important parts of a complete security posture.
Vulnerability Management & Penetration Testing
Finesse’s penetration testing services exceed conventional assessments, ensuring a thorough evaluation of an organization’s security posture. We specialize in various types of penetration testing, including:

Do not leave your enterprise exposed to evolving cyber threats. Finesse Cyberhub delivers proactive, intelligence-led security to keep you ahead.

As a regular participant at Gitex, how do you see its evolution over the years and supporting Finesse’s growth strategy? Since its inception, Finesse has participated regularly at Gitex. In the past, Gitex was mainly focused on the GCC, but as Dubai and the UAE have become global innovation hubs, Gitex has become one of...

Finesse is one of the most trusted software companies in the GCC, providing next-generation digital solutions and services to companies across all industry verticals. The key differentiators that separate Finesse from other system integration (SI) companies in the region are – Since Finesse’s founding in 2010, it has been guided by the vision to positively...

"*" indicates required fields
A : A traditional SOC (Security Operations Center) relies primarily on rules-based tools and human analysts to monitor and respond to threats. A Cognitive SOC (CSOC), such as the one operated by Finesse Cyberhub, integrates artificial intelligence, machine learning, and behavioral analytics to automate threat detection and response at a scale and speed that traditional SOCs cannot match. A CSOC greatly reduces false positives, accelerates Mean Time to Detect (MTTD), and ensures active threat hunting instead of only a reactive response.
A : The cost of managed SOC services in the UAE varies based on the size of the environment being monitored, the number of log sources and endpoints, the level of incident response support required, and the compliance frameworks to be addressed. Finesse Cyberhub offers flexible, scalable SOC as a service pricing, ideal for each client’s needs. Contact our team for a customized assessment and proposal.
A : Managed SOC services are perfect for organizations in highly regulated or high-risk sectors, including banking and financial services, healthcare, government and public sector, energy and utilities, telecommunications, retail, and logistics. Any UAE business that handles sensitive customer data, operates critical digital infrastructure, or must comply with NESA, NCA, or PDPL regulations will benefit from a managed SOC service.
A : Finesse Cyberhub’s CSOC is designed to support compliance with the UAE National Electronic Security Authority (NESA) controls, NCA Essential Cybersecurity Controls, UAE Personal Data Protection Law (PDPL), and ISO 27001. Our managed SOC services include built-in compliance monitoring, audit-ready reporting, and constant assessments to help clients demonstrate and maintain regulatory adherence.
A : A Managed Security Service Provider (MSSP) offers a broad range of outsourced security services, of which a managed SOC is one component. Finesse Cyberhub operates as both a specialist managed SOC service provider and a full MSSP, offering CISO advisory, VAPT, vulnerability management, compliance services, and identity security alongside core SOC operations, giving clients a single, integrated security partner.
A : Finesse Cyberhub’s managed SOC onboarding process usually achieves initial monitoring coverage within two to four weeks, with full operational deployment completed within six to eight weeks, depending on the complexity of the environment. Our team manages the entire onboarding process, including log source integration, SIEM tuning, and custom rule development.
For more details on Security Operations Center (SOC) Services Worldwide, contact us today at info@finessedirect.com
"*" indicates required fields